Are Wearable Drones Buzzing on the Horizon?
AUSTIN, Texas — Sometime in the near future, drones may be wearable and may even become our buddies — at least if one futurist has any say in the matter.
The wearable tech of the future might be able to perform many more functions than current technology can, from acting as a scout and tour guide in an unfamiliar city to being a rock-climbing companion, one expert said here at the South by Southwest (SXSW) Interactive festival.
That future isn’t so far away, said Adam Pruden, an interaction designer and tech futurist at design firm frog.”Drones are starting to behave like smartphones — and they’re also entering this era of post-smartphone capabilities,” Pruden said. “One day, drones may become an everyday household device.”
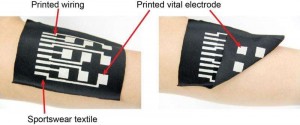
Wearable products
Drone technology is advancing rapidly, and these flying bots are already being used for a growing set of functions, from making agriculture more efficient to capturing dramatic video footage of a churning lava lake. Increasingly, drones are also being seen as a key way to deliver supplies to hard-to-reach areas during humanitarian crises. And as drones get smarter, their capabilities have begun to mirror those of smartphones, Pruden said.
Though wearable drones may seem far-fetched, at least one is almost on the market already: the wearable drone Nixie, which is a camera that launches from the wrist, is supposed to be released soon.
Pruden and his colleagues tried to envision what drones might look like in the future when wearable drones become more commonplace. First, they had to determine where drones could live on the body when they’re not in use.
“We have to find a place to put them when we’re not using them,” Pruden said.
Next, the team came up with myriad possible uses for the machines, from drones that carry intravenous drips to drone dog collars. In the end, they settled on four uses that seem the most promising.
The first, called Breathe, would be a pollution sensor and filter that sits passively on a person’s shoulder but deploys when pollution levels are high. The Breathe drone could hover in front of someone’s mouth and nose, cleaning the air they breathe. [See Images of the Wearable Drone Concepts]
Other devices could clip on to someone’s clothing or backpack and devise active games to play. The drone could even identify the proper route for a rock climber scaling a rock wall, the team said.
“It’s set to challenge the owner to continue to improve as they climb again and again,” Pruden said.
A personal tour guide, called the Flare, could attach to a clear wristband. When it’s time to investigate an unfamiliar city, the Flare could launch from the wrist and fly ahead, scouting out the best routes. When it returned, it could hover a few feet in front of the owner, pointing out interesting sites along the way.
The final concept, called Parasol, could act as a personalized weather drone that could be worn like jewelry or a belt buckle when not in use. If the bot were to detect impending precipitation or high levels of ultraviolent radiation, it could morph into protective gear (like an umbrella) to shield its owner from harm.
Drones of the future
Pruden predicts that wearable drones will be in use by around 2030. As these new objects proliferate, humans may create infrastructure to help them do their work, such as drone superhighways or charging stations that allow them to make long-distance journeys.
But these futuristic devices will likely have functions that are different from those on smartphones, which are basically used by just one person.
“They’re going to have to interact at many different scales — interact with other drones, other people and other objects,” Pruden said.
In a drone-filled world, the ever-present buzzing robots could affect human emotional states, Pruden said.
“We can anticipate that more technology and devices will be taking to the sky,” Pruden said. “We must carefully plan and design these objects to improve our lives rather than disrupting them.”
References:http://www.livescience.com/